What are security assessments?
To use the Data Communications Company (DCC) systems, all SEC Parties must undertake a User Security Assessment conducted by the User Competent Independent Organisation (CIO).
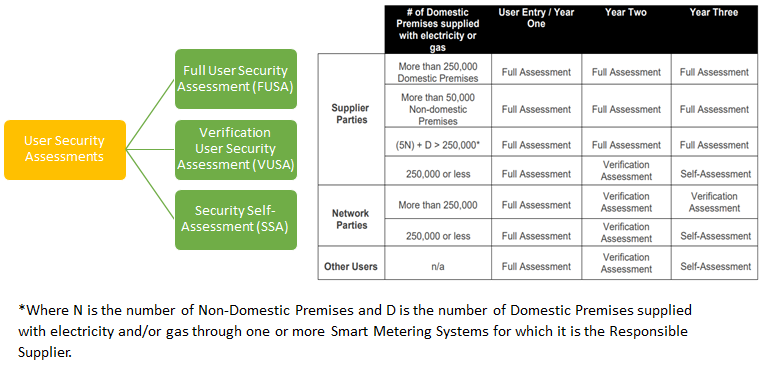
Security assessments take place in three-year cycles. Before becoming a DCC user, and on the first year of each cycle, SEC Parties must have an initial Full User Security Assessment (FUSA). After this, an annual Security Assessment is undertaken. The type of subsequent assessment will depend on your SEC Party type and the number of Smart Metering Systems it interacts with. The three types of security assessment are summarised below. For more information, please refer to the Security Controls Framework (SCF).
A FUSA is carried out by the User CIO to assess a User’s compliance with the obligations under SEC Sections G3 to G6, in respect to its User Role. The fieldwork should take between 3 and 10 working days; however, the duration largely depends on User preparedness, the number of observations and use of Shared Resource Provider vs Bespoke User System.
How do I prepare?
- Use the SCF and engage with SECAS and the User CIO.
A VUSA will address three key areas to determine the extent of any changes since the previous FUSA.
How do I prepare?
- Refer to the SCF Guidance and engage with SECAS and the User CIO.
An SSA is carried out by the User to identify any material increase in the security risk since the last time either a FUSA or VUSA was carried out. The assessment focuses on those areas exposed to any material increase in security risks as indicated by a User’s obligation to identify and manage risk (in accordance with G5.14).
How do I prepare?
- Submit the Book an Assessment form for review, in corroboration with the User CIO prior to presentation to the SSC.
- Refer to the list of User questions in the SCF.
Three Year Cycle
Why do I need to have a security assessment?
User Security Assessments assure the Security Sub-Committee (SSC) and the SEC Panel that:
- Users have secure end-to-end Smart Metering Systems;
- any security risks are mitigated and resolved quickly; and
- there isn’t any one point of compromise to the Smart Metering ecosystem.
Who will conduct my assessment?
Deloitte LLP is currently appointed as the User CIO and performs the User Security Assessments on behalf of the SEC Panel. The User CIO assess whether SEC Parties and DCC Users comply with the obligations in SEC Sections G3 to G6.
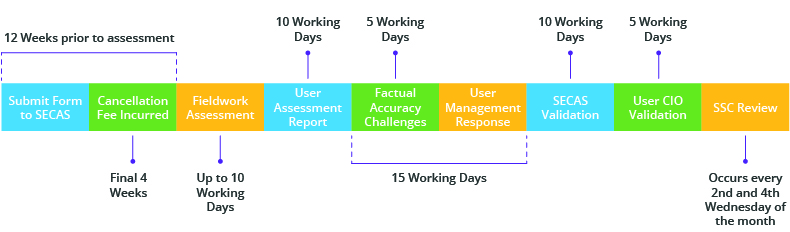
Overview of the Process
What happens next?
The SSC will review the assessment and set an assurance status based on a Party’s compliance with the obligations in SEC Sections G3 – G6. There are four possible assurance statuses:
- “Approved”
- “Approved, subject to the Party…”
- “Deferred”
- and “Rejected”.
Once a SEC Party’s assessment has been fully approved by the SSC, they are able to complete the User Entry Process and use DCC Live systems. If there are outstanding observations from the assessment, the SSC may request further evidence from the SEC Party before approving them to go Live. If there are many outstanding observations and the SSC is not satisfied that the security risks will be remediated, the SSC may request that the SEC Party has a Follow-Up Assessment.
Costs and cancellation fees
This cost is indicative (Rate Cards below) as the User CIO will only charge the SEC Party or DCC User for the actual number of days used to undertake the User Security Assessment and produce the User Security Assessment Report. The final cost of the User Security Assessment will appear within your DCC monthly charges (likely as a new line) after this work has been invoiced by the User CIO.
If you wish to reschedule your User Security Assessment, then you must do so at least four weeks in advance of the assessment date. If you provide less than four weeks’ notice, then you can be charged 25% of the total cost of the assessment.
